Single sign-on
Contents
Learn how single sign-on is supported in Genesys Engage.
Most Genesys Engage cloud applications allow a logged-in user to navigate across those applications without prompting for credentials again. It can also be configured to use SAML 2.0 for integrations with third-party identity providers such as Okta or Google. There are many advantages to enabling single sign-on (SSO) in Genesys Engage cloud—for example:
- Users need to remember only one password.
- User credentials are managed by a third-party identity provider.
- Users must have multi-factor authentication by a third-party identity provider for additional security.
- Users only need to log in once to gain access to Genesys Engage cloud applications that have SSO enabled and non-Genesys applications that use the same identity provider.
SSO support by application
View which Genesys Engage cloud applications support SSO.
| Applications | Single Sign On Support | Notes |
|---|---|---|
| Agent Desktop | Yes | |
| Agent Setup | Yes | |
| Callback | Yes | |
| Cloud Data Download Service | Yes | |
| CX Contact | Yes | |
| Designer | Yes | |
| Developer Console | Yes | |
| Genesys CX Insights | Yes | Supported in version 9.0.013.0+. Contact your Genesys representative to enable. |
| Genesys Softphone | Yes | |
| Screen Recording | Yes | Supported in Agent Desktop version 9, but not with custom desktops. |
| Real-Time Reporting (Pulse) | Yes | Supported in Real-Time Reporting version 9. |
| Gplus Adapter Salesforce | Yes | |
| Recording, Quality Management and Speech Analytics | Future Roadmap | |
| Workforce Management | Yes | Not supported for supervisor accounts for administrative activities. |
| Agent Scripting Administration | No | |
| Interactive Insights | No | |
| Outbound | No | |
| Platform Administration (GAX)
Includes plug-ins like eServices Manager and IVR Administration |
No | |
| WebRTC | Yes |
Configuring SSO in Genesys Engage
To enable Single Sign-On for your environments, see Single Sign-On in Agent Setup.
If you're planning to enable SSO, consider the following conventions for creating users:
- The domain declared in the identity provider metadata should be part of the user name stored within Genesys, to create the most seamless experience. (Example: john@mycompany.com) Otherwise, users would need to enter a Tenant or enter the domain before their username. (Example: mycompany\john)
- The username provisioned within Genesys Engage cloud should match the username in the external identity provider.
Configuring SSO in the identity provider
Genesys Engage cloud must be defined as an application within the identity provider to support the SSO integration.
Genesys Engage cloud supports the SAML 2.0 protocol as a standard interface to identity providers, and has successfully validated with popular IdPs, including Okta and Ping. Other identity providers can be supported provided they comply with SAML 2.0 and you validate the integration before using in production.
How does SSO work for users?
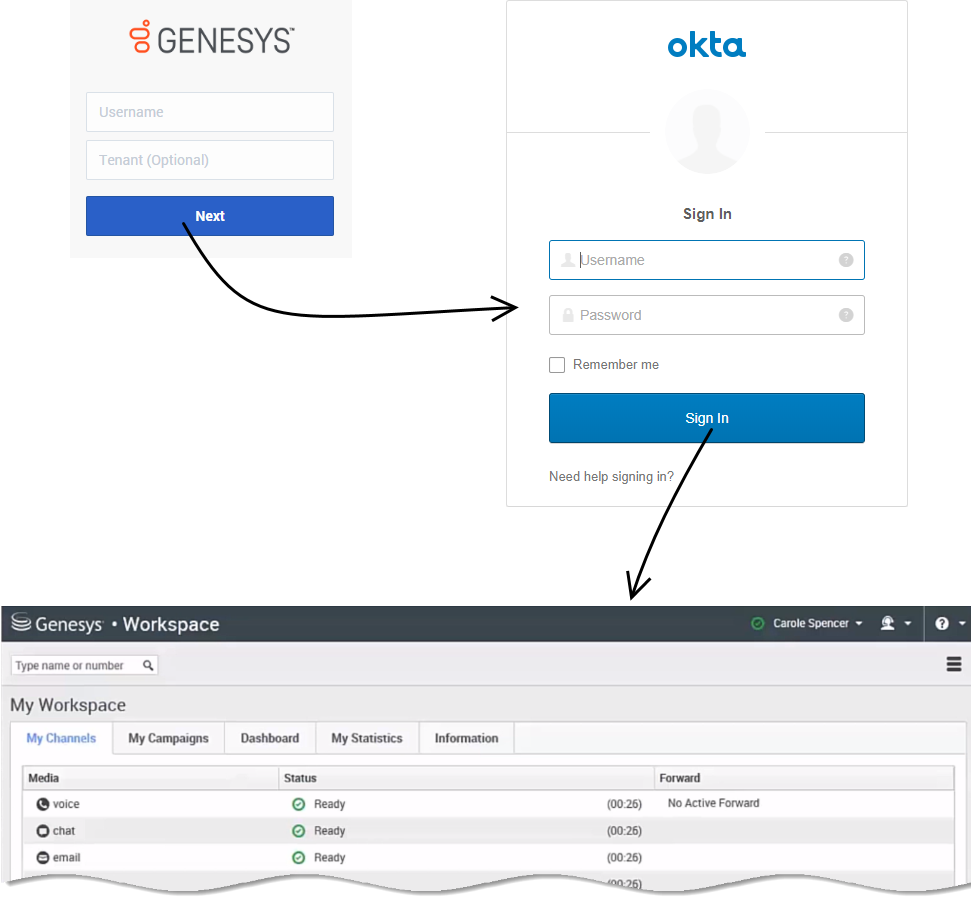
Let's look at the login process for Agent Desktop with SSO enabled and Okta configured as the third-party identity provider. Note: The login flow is the same for all supported identity providers.
First, click the Agent Desktop icon in Genesys Portal and enter your username. You must log in to the application even though you're already logged in to your workstation.
Click Next. Genesys redirects you to Okta where you're prompted to enter your username and password. Once you log in with Okta, you're redirected back to Agent Desktop and automatically logged in. Alternatively, if you are already logged in with Okta when you click Next, Genesys skips the Okta login and automatically logs you in to Agent Desktop.
Now that you're authenticated with the identity provider, you can choose any SSO-enabled application from Genesys Portal and you'll be automatically logged in without entering your credentials.
If you happen to close all browser tabs without logging out of the applications, you will remain logged in for five minutes. If a second window or browser is opened after five minutes, to either the same application or any other SSO-enabled application, you will once again be prompted for your credentials.